Last month, I put the finishing touches on three different online training modules for the industry-serving, non-profit Automotive Management Institute (AMi). These modules are: Website and SEO Basics, Social Media Management and Video Production, and Email Security Basics. Each are now available online, along with over 100 others at www.amionline.org. I’ll give you a sneak peek into Email Security Basics below, but first I want to put in my plug for AMi.
The Next Generation
AMi has evolved into a state-of-the-art training organization with the addition of their online training modules. The recent launch of the next generation of AMi is a significant event for collision repair and mechanical shop business owners and managers. The new AMi offers relevant front office and management education, including career paths, certificates and professional designations. On the collision side, AMi now offers a certificate in Collision Repair Customer Service, and three professional designations: Collision Repair Office Manager, General Manager and Master General Manager.
AMi collaborates with industry training providers to accredit their programs toward their certificates and designations. Access to AMi’s 100-plus online courses is available through their my AMi learning management system, which includes industry-relevant content from myself and colleagues Mike Anderson, Michael Graham, Frank LaViola and many others. The new AMi is designed to improve repair businesses’ front office and management efficiency, accuracy and communications, resulting in better CSI, net promoter scores and profitability. Exciting, huh?
Email Security Basics
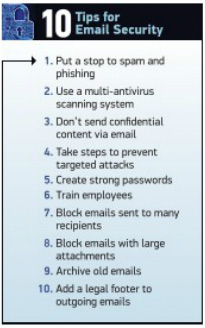
One of the many important core courses offered now at www.amionline.org is my Email Security Basics module, where I discuss the fact that crimes are being committed online every second of every day. These criminals are seeking vulnerabilities found on your website, computers, tablets and phones to access your personal information, steal business trade secrets or pursue other exploitive or malicious purposes. People who do this are often referred to as hackers. The tools and methods these people use include:
- Spam
- Phishing
- Malware
- Hacking
I’ll describe each of these briefly below, and you can get the full course at AMI.
 Spam. The first method is electronic “junk mail,” also known as spam or unsolicited bulk email. This method involves numerous recipients receiving identical messages. Not only are spam emails annoying, they can be harmful. Spam may have attachments containing harmful computer viruses, also known as malware. Many also include hidden or disguised links to something that looks legitimate. But beware, these links can lead to phishing websites or sites hosting malware that can be installed on your computer just by visiting the sites. Keep in mind, these criminals are good at making these emails look legitimate in an attempt to get you to open them and click on the attachments or links.
Spam. The first method is electronic “junk mail,” also known as spam or unsolicited bulk email. This method involves numerous recipients receiving identical messages. Not only are spam emails annoying, they can be harmful. Spam may have attachments containing harmful computer viruses, also known as malware. Many also include hidden or disguised links to something that looks legitimate. But beware, these links can lead to phishing websites or sites hosting malware that can be installed on your computer just by visiting the sites. Keep in mind, these criminals are good at making these emails look legitimate in an attempt to get you to open them and click on the attachments or links.
Phishing. Spam is frequently used to direct people to fake websites or phishing websites. These websites are designed to look like they’re from banks, schools, PayPal, eBay, Amazon, newspapers, domain registration services and even the IRS. When unsuspecting people are baited into visiting these sites, the criminals go “phishing” for private information, such as credit card numbers, social security numbers, bank passwords and much more. But, as you should know, none of these services will ever ask you for personal information in this manner! And phishing isn’t exclusive to email. Social media sites like Facebook, Twitter and Instagram can also be used to bait and catch unsuspecting victims.
Malware. Malicious software, or malware, is a term used to describe many techniques criminals use for nefarious purposes. It includes:
- Viruses
- Worms
- Trojan horses
- Ransomware
- Spyware
- Scareware
My new AMI training module describes each of these, and the threats they pose, in more detail.
Hacking. A hacker, in the context of computer security, is someone who looks for weaknesses in computer systems and networks. They have different motivations for what drives them to hack into a system. Some hire hackers to find weaknesses in their own business systems and protect their systems from threats. Some hackers do it to protest the actions of a company or government. Other hackers are paid to access accounts, discover passwords and break into lucrative accounts. Others do it for the challenge or for the pure enjoyment of it, much like a hobby. Mostly, hackers look for easy targets.
Included in this AMI Email Security Basics module is a suggested email policy document and an email etiquette guidelines document. If you would like to obtain a copy of these, visit www.optimaautomotive.com/contact-website-specialist/.